Objection环境、自动化分析和插件
在上一章搭建好了frida和objection环境,本章主要学习一下这些工具怎么使用
frida和objection工具的使用
关于这两个工具的使用,可以参考roysue大佬这篇文章中的内存漫游和hook部分。
这里只补充记录一点细节:
frida和objection都提供的有help
frida -h # frida打开help的命令 objection --help # objection打开help的命令检索

也可以使用cat命令检索objectin.log的文件
──(kali㉿kali)-[~] └─$ cat .objection/objection.log | grep -i frida frida Frida Version 12.8.0 Frida Heap Size 16.9 MiB frida Frida Version 12.8.0 Frida Heap Size 16.9 MiB frida Frida Version 12.8.0 Frida Heap Size 28.4 MiB help frida Command: frida Usage: frida Displays information about Frida. This includes the version of the Frida gadget, frida frida-agent-64.so 0x743735e000 20021248 (19.1 MiB) /data/local/tmp/re.frida.server/frida-agent-64.so frida-agent-64.so 0x7435ca6000 20021248 (19.1 MiB) /data/local/tmp/re.frida.server/frida-agent-64.so有时候frida-server连接错误需要重启
|marlin:/data/local/tmp # netstat -tulpn | grep :8888 tcp 0 0 0.0.0.0:8888 0.0.0.0:* LISTEN 9711/fs-12 tcp 40 0 127.0.0.1:41385 127.0.0.1:8888 ESTABLISHED 27125/com.cz.babySister tcp 0 0 127.0.0.1:8888 127.0.0.1:41385 ESTABLISHED 9711/fs-12 marlin:/data/local/tmp # kill -9 9711 marlin:/data/local/tmp # ./fs-12 -l 0.0.0.0:8888 & [2] 4204 [1] - Killed ./fs -l 0.0.0.0:8888检索activities,如果app没有做限制可以绕过登录直接跳转到目标activity
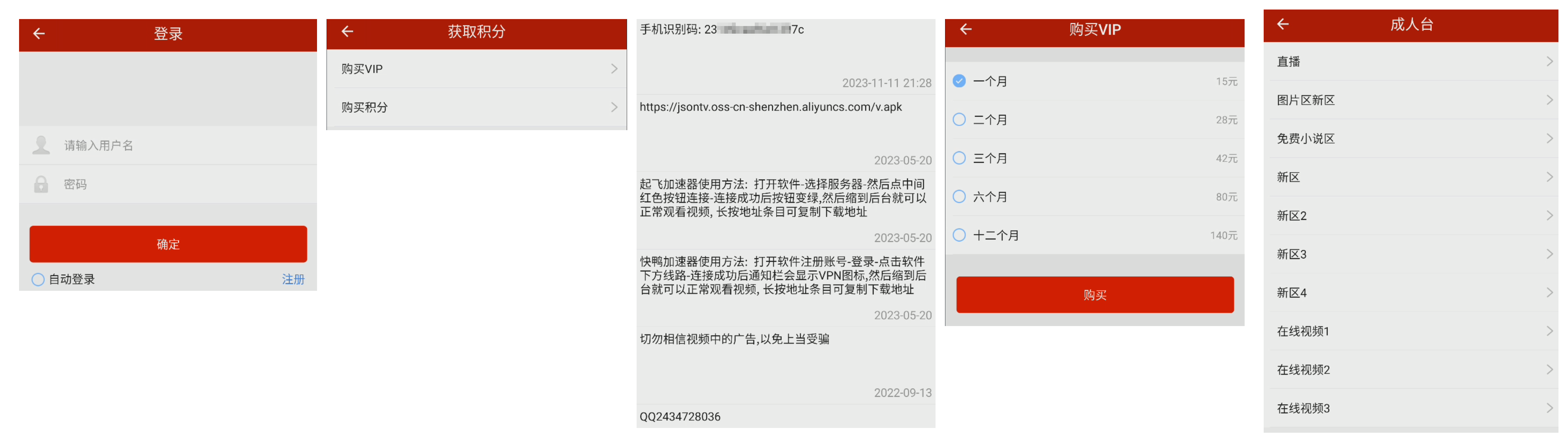
┌──(kali㉿kali)-[~] └─$ objection -N -h 192.168.1.7 -p 8888 -g com.cz.babySister explore Using networked device @`192.168.1.7:8888` Agent injected and responds ok! _ _ _ _ ___| |_|_|___ ___| |_|_|___ ___ | . | . | | -_| _| _| | . | | |___|___| |___|___|_| |_|___|_|_| |___|(object)inject(ion) v1.8.4 Runtime Mobile Exploration by: @leonjza from @sensepost [tab] for command suggestions com.cz.babySister on (google: 10) [net] # android hooking list activities com.alipay.sdk.app.AlipayResultActivity com.alipay.sdk.app.H5AuthActivity com.alipay.sdk.app.H5OpenAuthActivity com.alipay.sdk.app.H5PayActivity ... com.cz.babySister.wxapi.WXEntryActivity com.tencent.connect.common.AssistActivity com.tencent.smtt.sdk.VideoActivity com.tencent.tauth.AuthActivity Found 55 classes com.cz.babySister on (google: 10) [net] # android intent launch_activity com.cz.babySister.activity.MessageActivity (agent) Starting activity com.cz.babySister.activity.MessageActivity... (agent) Activity successfully asked to start. com.cz.babySister on (google: 10) [net] # android intent launch_activity com.cz.babySister.activity.JiFenActivity (agent) Starting activity com.cz.babySister.activity.JiFenActivity... (agent) Activity successfully asked to start. com.cz.babySister on (google: 10) [net] # com.cz.babySister on (google: 10) [net] # android intent launch_activity com.cz.babySister.wxapi.WXEntryActivity (agent) Starting activity com.cz.babySister.wxapi.WXEntryActivity... (agent) Activity successfully asked to start. com.cz.babySister on (google: 10) [net] # android intent launch_activity com.cz.babySister.activity.ChengRenVideoActivity (agent) Starting activity com.cz.babySister.activity.ChengRenVideoActivity... (agent) Activity successfully asked to start. com.cz.babySister on (google: 10) [net] #
就像这个如果app没有做限制的话,就算没有登陆也可以在这些activity之间进行跳转
不过这种现在比较少了,大部分app都做了处理
用frida连接手机的时候,也可以通过
jnettop查看连接的ip、端口、流量大小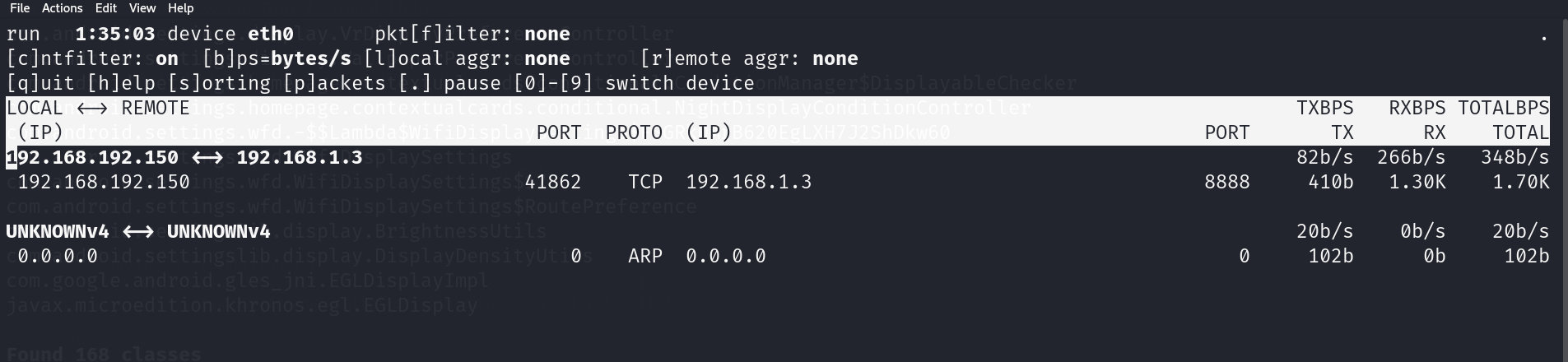
取消jobs的命令是
jobs kill job IDcom.android.settings on (google: 10) [net] # jobs list Job ID Hooks Type ----------- ----- ----------------------------------------------------------- 7292iblia76 63 watch-class for: android.bluetooth.BluetoothDevice k24tk3ywand 1 watch-method for: android.bluetooth.BluetoothDevice.getName iargrzfrte 6 watch-method for: java.io.File.$init com.android.settings on (google: 10) [net] # jobs kill 7292iblia76 com.android.settings on (google: 10) [net] # jobs list Job ID Hooks Type ----------- ----- ----------------------------------------------------------- k24tk3ywand 1 watch-method for: android.bluetooth.BluetoothDevice.getName iargrzfrte 6 watch-method for: java.io.File.$init对基础库的hook可以得到非常多的信息
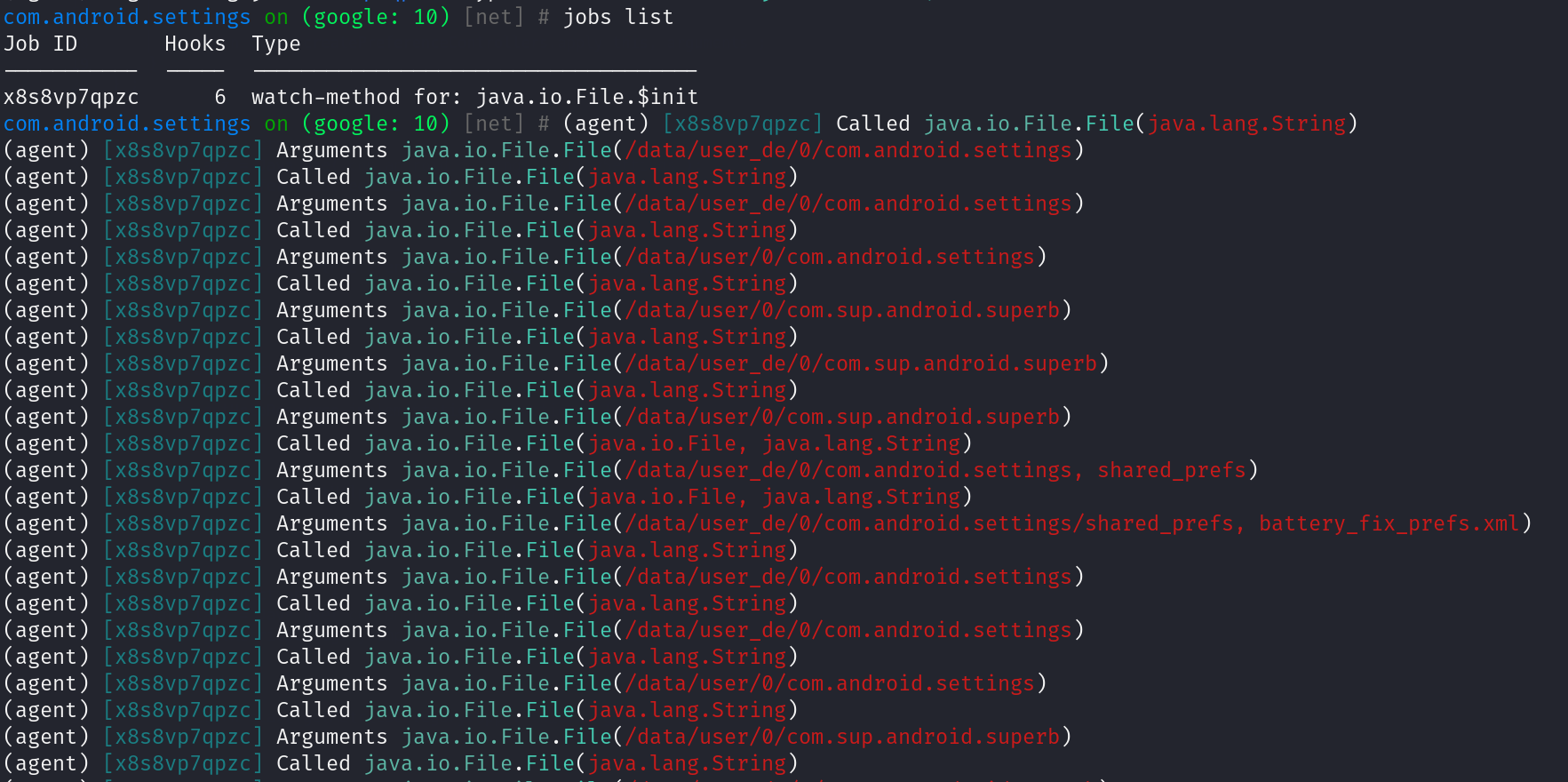
com.android.settings on (google: 10) [net] # android hooking watch class_method java.io.File.$init --dump-args (agent) Attempting to watch class java.io.File and method $init. (agent) Hooking java.io.File.$init(java.io.File, java.lang.String) (agent) Hooking java.io.File.$init(java.lang.String) (agent) Hooking java.io.File.$init(java.lang.String, int) (agent) Hooking java.io.File.$init(java.lang.String, java.io.File) (agent) Hooking java.io.File.$init(java.lang.String, java.lang.String) (agent) Hooking java.io.File.$init(java.net.URI) (agent) Registering job x8s8vp7qpzc. Type: watch-method for: java.io.File.$init com.android.settings on (google: 10) [net] # jobs list Job ID Hooks Type ----------- ----- ------------------------------------ x8s8vp7qpzc 6 watch-method for: java.io.File.$init例如:在设置里面执行操作
hook了File构造器的所有重载,,在设置界面随意进出几个子设置界面,可以看到命中很多次该方法的不同重载,每次参数的值也都不同
插件使用
objection和frida都可以加载插件使用。具体情况看插件的readme会说明使用方法
Wallbreaker使用
下载插件,然后加载就可以使用了
┌──(kali㉿kali)-[~/Downloads/Wallbreaker]
└─$ objection -N -h 192.168.1.3 -p 8888 -g com.android.settings explore
Using networked device @`192.168.1.3:8888`
Agent injected and responds ok!
_ _ _ _
___| |_|_|___ ___| |_|_|___ ___
| . | . | | -_| _| _| | . | |
|___|___| |___|___|_| |_|___|_|_|
|___|(object)inject(ion) v1.8.4
Runtime Mobile Exploration
by: @leonjza from @sensepost
[tab] for command suggestions
com.android.settings on (google: 10) [net] # plugin load /home/kali/Downloads/Wallbreaker
Loaded plugin: wallbreaker
加载完就可以使用了
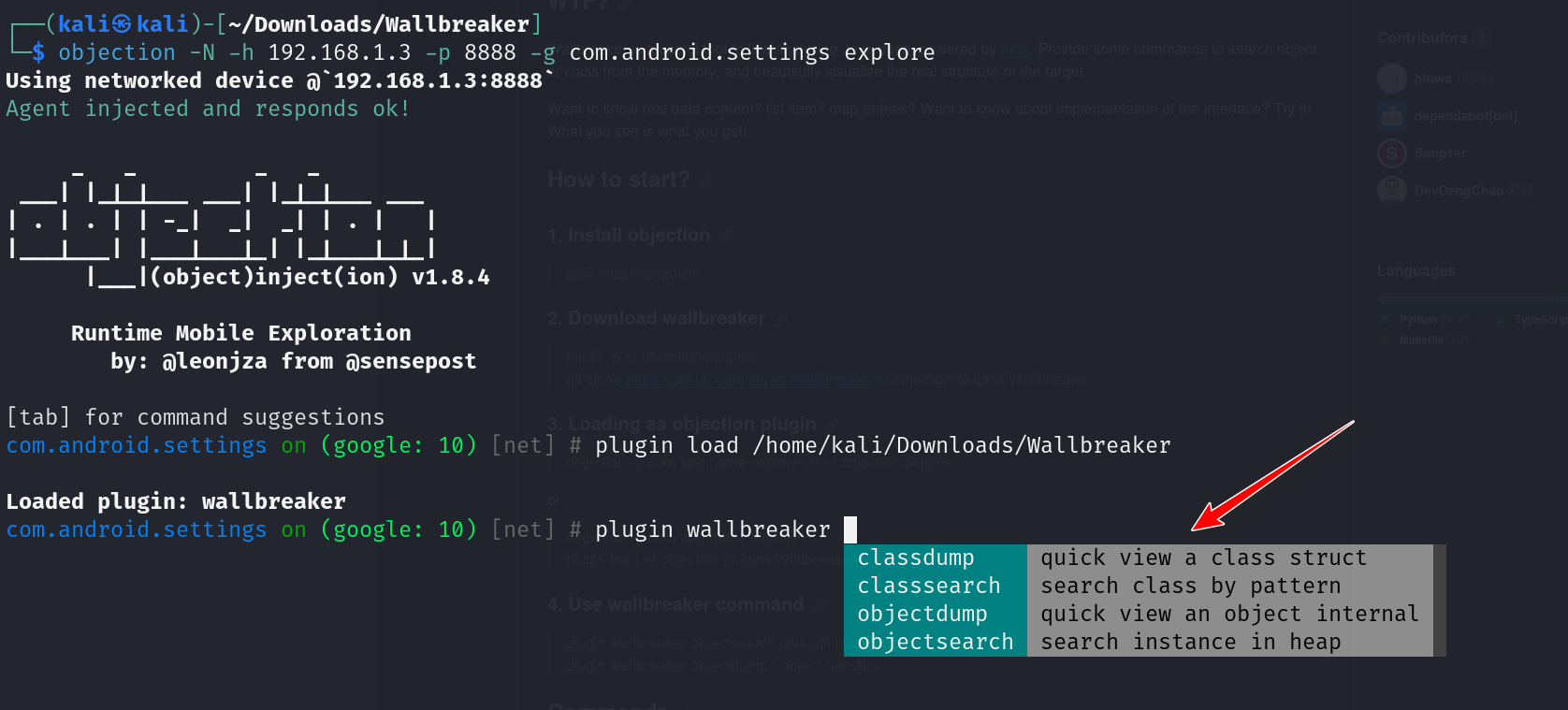
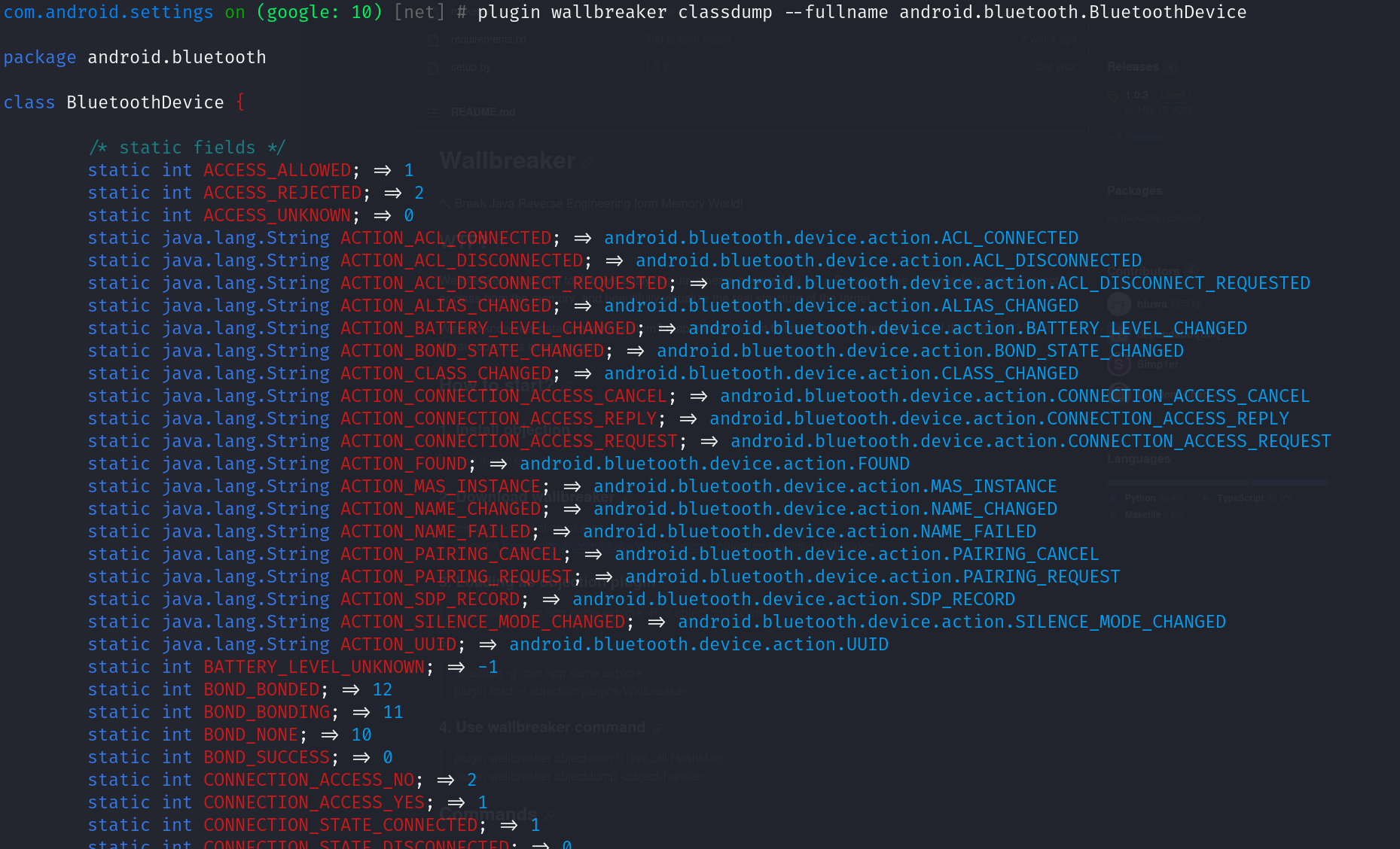
- 可以查看感兴趣的类的包名、成员变量和属性信息等等,可以对一个类进行一个基本的了解
frida-dexdump脱壳插件
pip3 install frida-dexdump
下载的时候我们安装一个带壳的apk等下测试
安装完之后运行
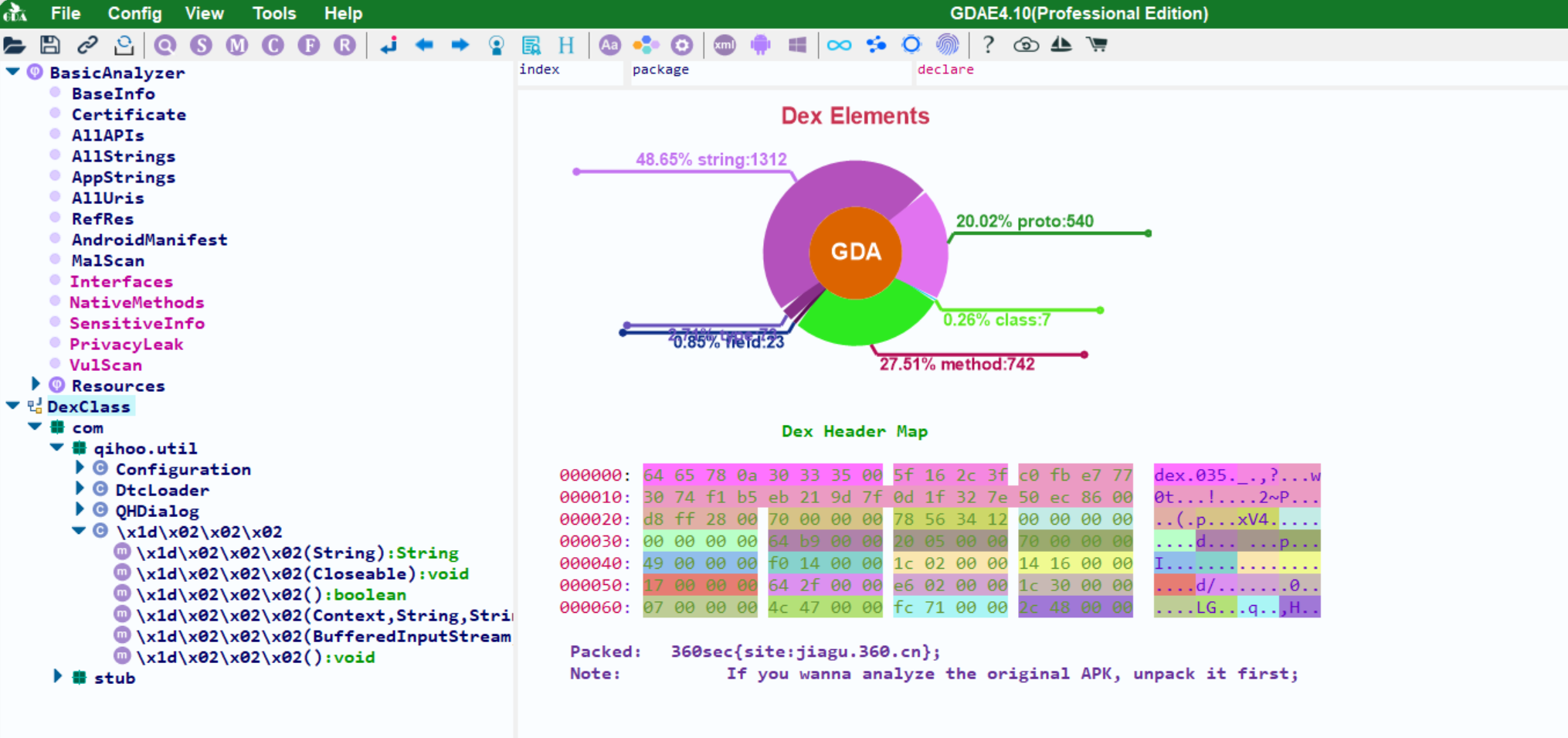
用objection检索一下包中的类名:大部分都已经被壳替换掉了
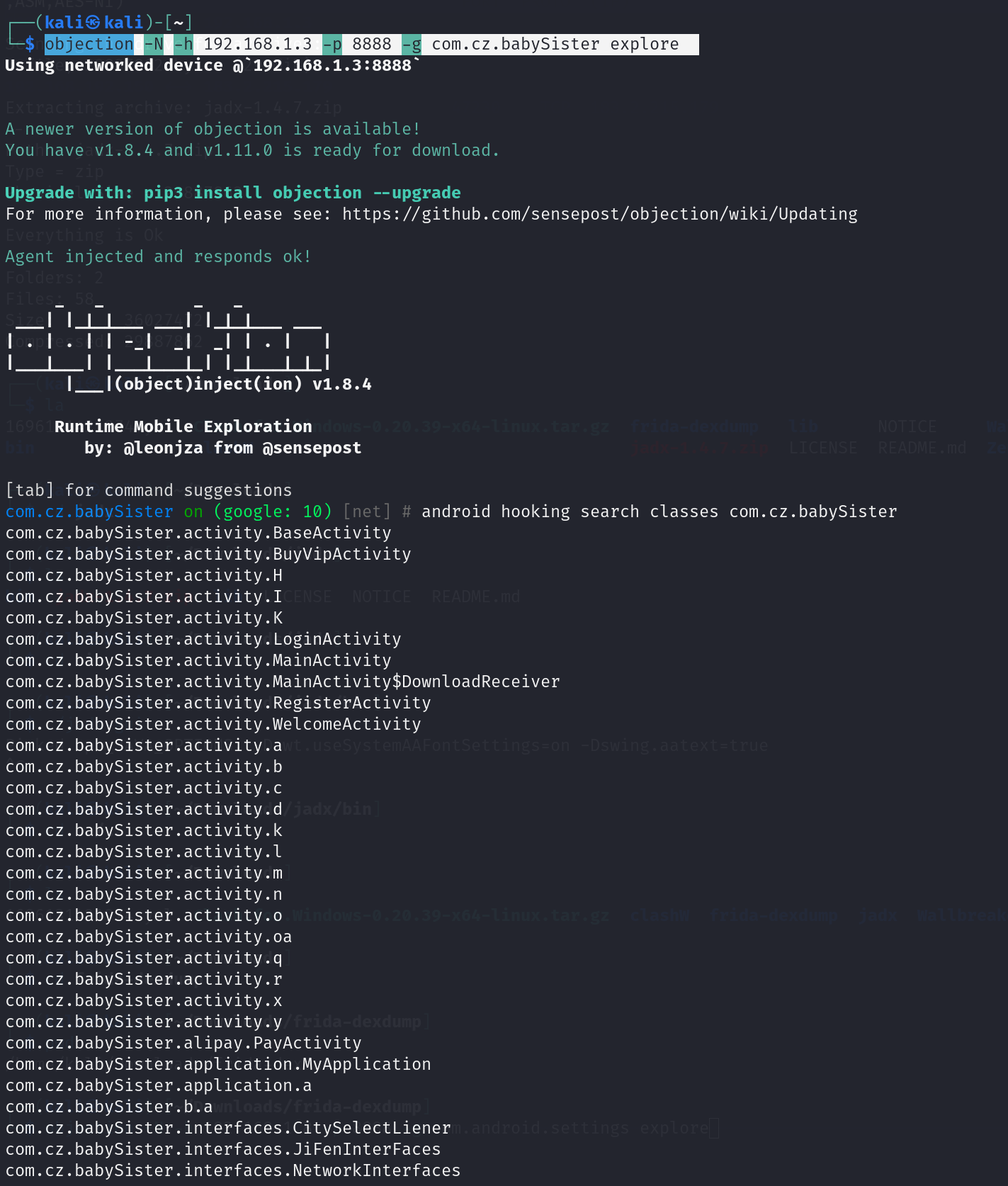
- com.cz.babySister.alipay.PayActivity(阿里支付)、com.cz.babySister.interfaces.JiFenInterFaces(积分),可以看到一些登陆注册、支付等activity,不过大部分都被无意义的字母替换掉了
下载完使用脱壳工具frida-dexdump脱壳
关于脱壳命令:
- 指定App的应用名称:frida-dexdump -U -n 保利票务
- 指定App的应用进程ID:frida-dexdump -U -p 3302
- 指定App的应用包名:frida-dexdump -U -f com.iCitySuzhou.suzhou001
┌──(kali㉿kali)-[~/Downloads] └─$ frida-dexdump -H 192.168.1.3:8888 -f com.cz.babySister ----------------------------------------------------------------------------------------------------------------------------------- __ _ _ _ _ / _|_ __(_) __| | __ _ __| | _____ ____| |_ _ _ __ ___ _ __ | |_| '__| |/ _` |/ _` |_____ / _` |/ _ \ \/ / _` | | | | '_ ` _ \| '_ \ | _| | | | (_| | (_| |_____| (_| | __/> < (_| | |_| | | | | | | |_) | |_| |_| |_|\__,_|\__,_| \__,_|\___/_/\_\__,_|\__,_|_| |_| |_| .__/ |_| https://github.com/hluwa/frida-dexdump ----------------------------------------------------------------------------------------------------------------------------------- Spawning `com.cz.babySister`... INFO:Agent:DexDumpAgent<Connection(pid=Session(pid=27125), connected:True), attached=True>: Attach. INFO:frida-dexdump:Waiting 5s... INFO:frida-dexdump:[+] Searching... INFO:frida-dexdump:[*] Successful found 16 dex, used 13 time. INFO:frida-dexdump:[+] Starting dump to '/home/kali/Downloads/com.cz.babySister'... INFO:frida-dexdump:[+] DexMd5=e00b57c04166adc8236012e872f01df4, SavePath=/home/kali/Downloads/com.cz.babySister/classes.dex, DexSize=0x9e74c INFO:frida-dexdump:[+] DexMd5=735418c3b52a60e8497a6746cdd940a0, SavePath=/home/kali/Downloads/com.cz.babySister/classes02.dex, DexSize=0x6c022c INFO:frida-dexdump:[+] DexMd5=425e63748a44957ba9000e325479c997, SavePath=/home/kali/Downloads/com.cz.babySister/classes03.dex, DexSize=0x551eb4 INFO:frida-dexdump:[+] DexMd5=a2fa46881e6a15401a35e782d91a5c30, SavePath=/home/kali/Downloads/com.cz.babySister/classes04.dex, DexSize=0xba28 INFO:frida-dexdump:[+] DexMd5=c155bf12df19e0f311c4859bb3690be0, SavePath=/home/kali/Downloads/com.cz.babySister/classes05.dex, DexSize=0x35a70 INFO:frida-dexdump:[+] DexMd5=f1771b68f5f9b168b79ff59ae2daabe4, SavePath=/home/kali/Downloads/com.cz.babySister/classes06.dex, DexSize=0x11c INFO:frida-dexdump:[+] DexMd5=7b3196f88e671b759185123f53ac9d13, SavePath=/home/kali/Downloads/com.cz.babySister/classes07.dex, DexSize=0xba28 Set read permission for memory range: 0x77e532add0-0x77e56d4000 Set read permission for memory range: 0x77e532add0-0x77e57d0000 Set read permission for memory range: 0x77e532add0-0x77e5831000 ERROR:frida-dexdump:[-] Error: access violation accessing 0x77e53ee000 at frida/runtime/core.js:144 at frida/runtime/message-dispatcher.js:15 at c (frida/runtime/message-dispatcher.js:25): {'addr': '0x77e532add0', 'size': 5609016} Traceback (most recent call last): File "/home/kali/.pyenv/versions/3.8.0/lib/python3.8/site-packages/frida_dexdump/__main__.py", line 81, in dump bs = self.agent.memory_dump(dex['addr'], dex['size']) File "/home/kali/.pyenv/versions/3.8.0/lib/python3.8/site-packages/frida_dexdump/agent/__init__.py", line 24, in memory_dump return self._rpc.memorydump(base, size) File "/home/kali/.pyenv/versions/3.8.0/lib/python3.8/site-packages/frida/core.py", line 401, in method return script._rpc_request('call', js_name, args, **kwargs) File "/home/kali/.pyenv/versions/3.8.0/lib/python3.8/site-packages/frida/core.py", line 26, in wrapper return f(*args, **kwargs) File "/home/kali/.pyenv/versions/3.8.0/lib/python3.8/site-packages/frida/core.py", line 333, in _rpc_request raise result[2] frida.core.RPCException: Error: access violation accessing 0x77e53ee000 at frida/runtime/core.js:144 at frida/runtime/message-dispatcher.js:15 at c (frida/runtime/message-dispatcher.js:25) INFO:frida-dexdump:[+] DexMd5=8345c73b46814e1384ff8462248b23af, SavePath=/home/kali/Downloads/com.cz.babySister/classes08.dex, DexSize=0x695a8 INFO:frida-dexdump:[+] DexMd5=ecf7cddd075183ac84db1677966211d0, SavePath=/home/kali/Downloads/com.cz.babySister/classes09.dex, DexSize=0x1274a4 INFO:frida-dexdump:[+] DexMd5=e920130e06b5687afe980ddb8e3b4425, SavePath=/home/kali/Downloads/com.cz.babySister/classes10.dex, DexSize=0x1557b4 INFO:frida-dexdump:[+] DexMd5=fd1b06e77f97579a960bb5029b46cc33, SavePath=/home/kali/Downloads/com.cz.babySister/classes11.dex, DexSize=0x325530 INFO:frida-dexdump:[+] DexMd5=7e343cbc45b618d05182d74bd61826b2, SavePath=/home/kali/Downloads/com.cz.babySister/classes12.dex, DexSize=0x4b7700 INFO:frida-dexdump:[+] DexMd5=2dd14f384bfe4741e5a9463e12c79c89, SavePath=/home/kali/Downloads/com.cz.babySister/classes13.dex, DexSize=0xecfc INFO:frida-dexdump:[+] DexMd5=b93f8047ed660629c2efe0aef2bbe0e4, SavePath=/home/kali/Downloads/com.cz.babySister/classes14.dex, DexSize=0x63194 INFO:frida-dexdump:[*] All done...
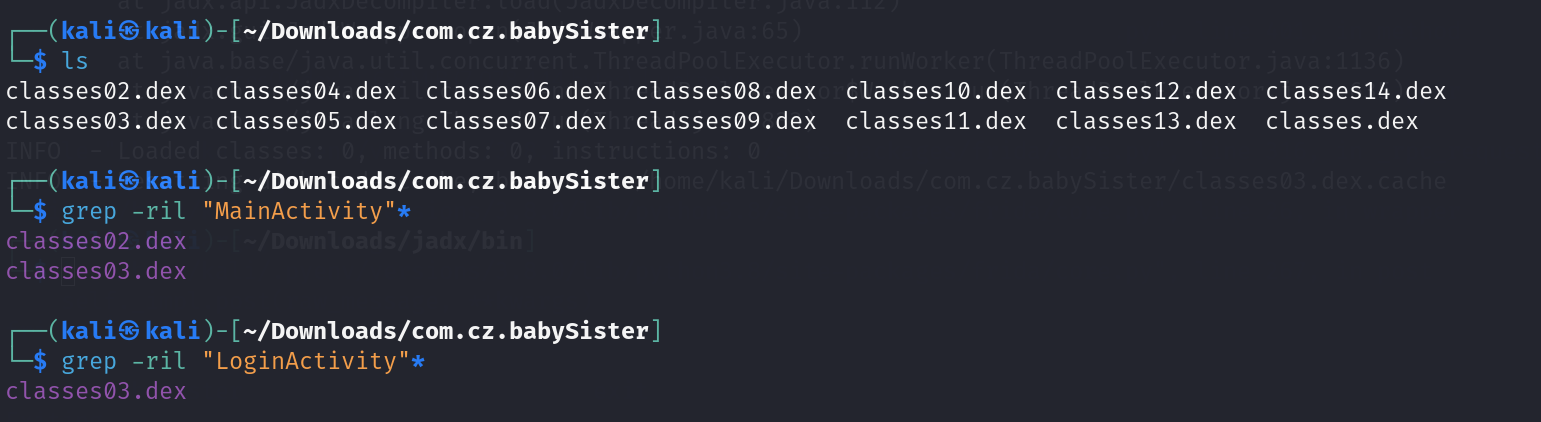
脱完壳之后可以看到脱出来了很多个dex文件
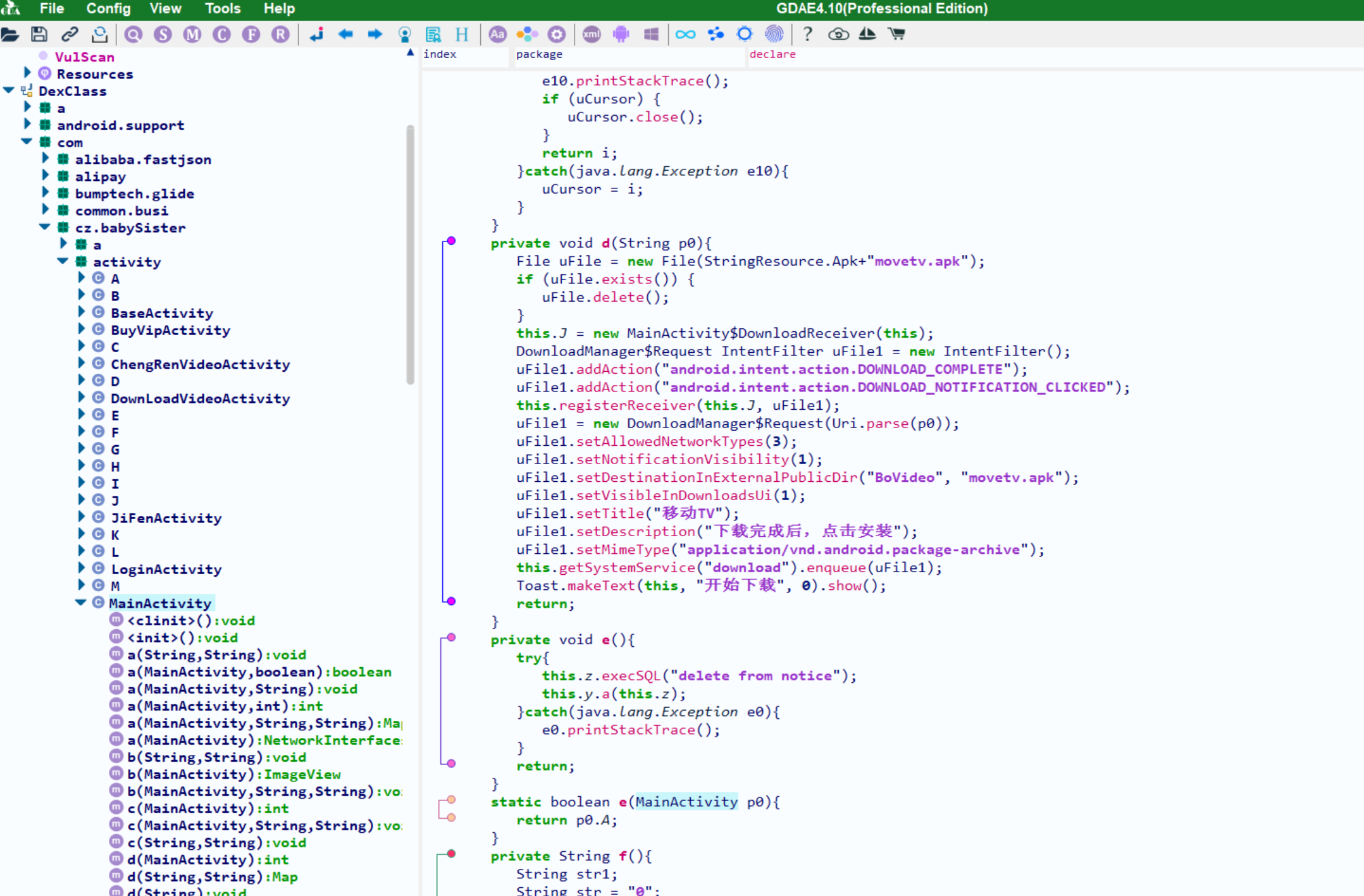
我们搜索一下MainActivity在哪个文件里面
使用jadx打开这两个dex文件
打开失败:checksum出错了
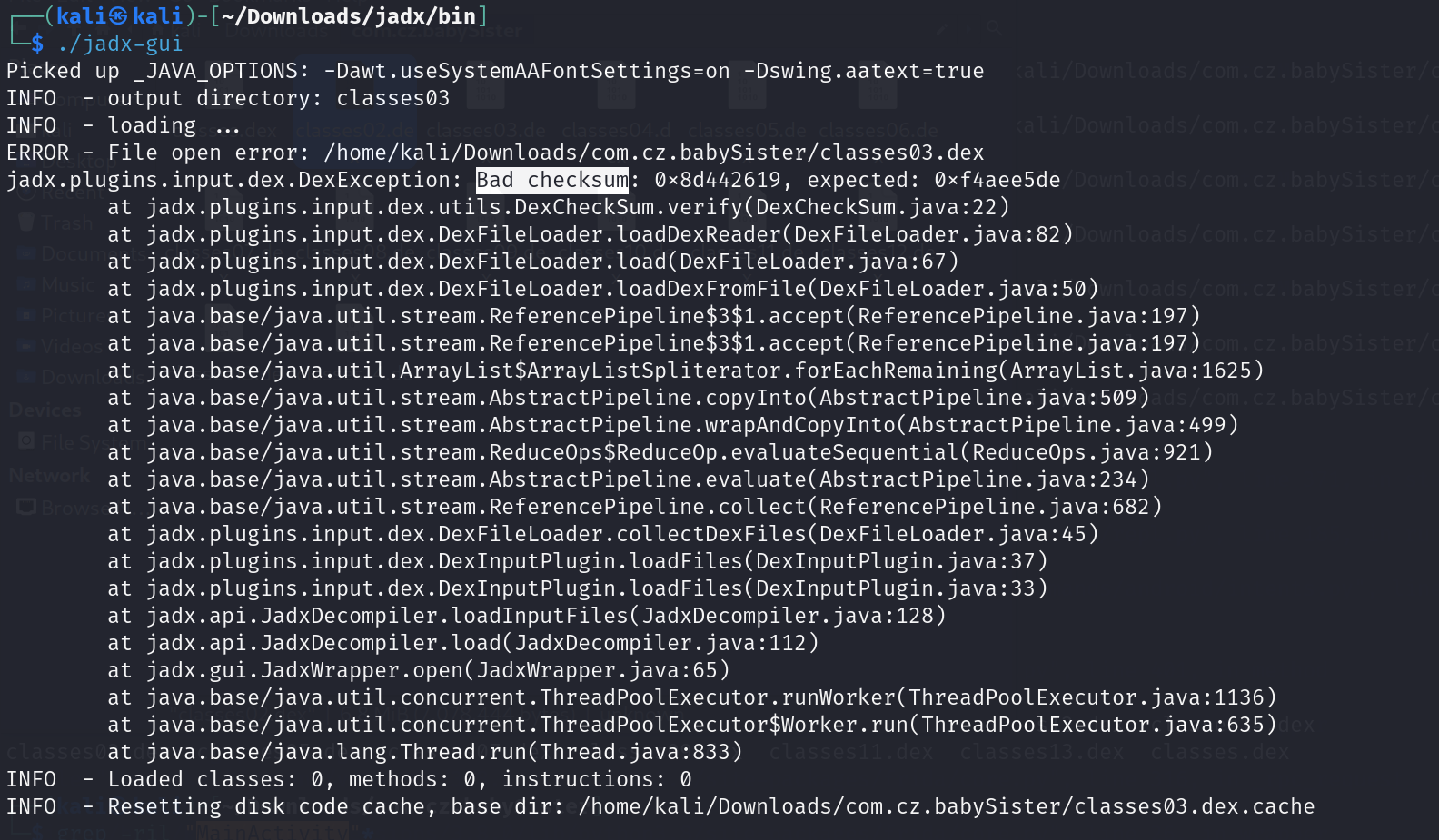
那暂时先把checksum关掉
位置:File(文件 )> Preferences(首选项):快捷键(CTRL+shift+P)
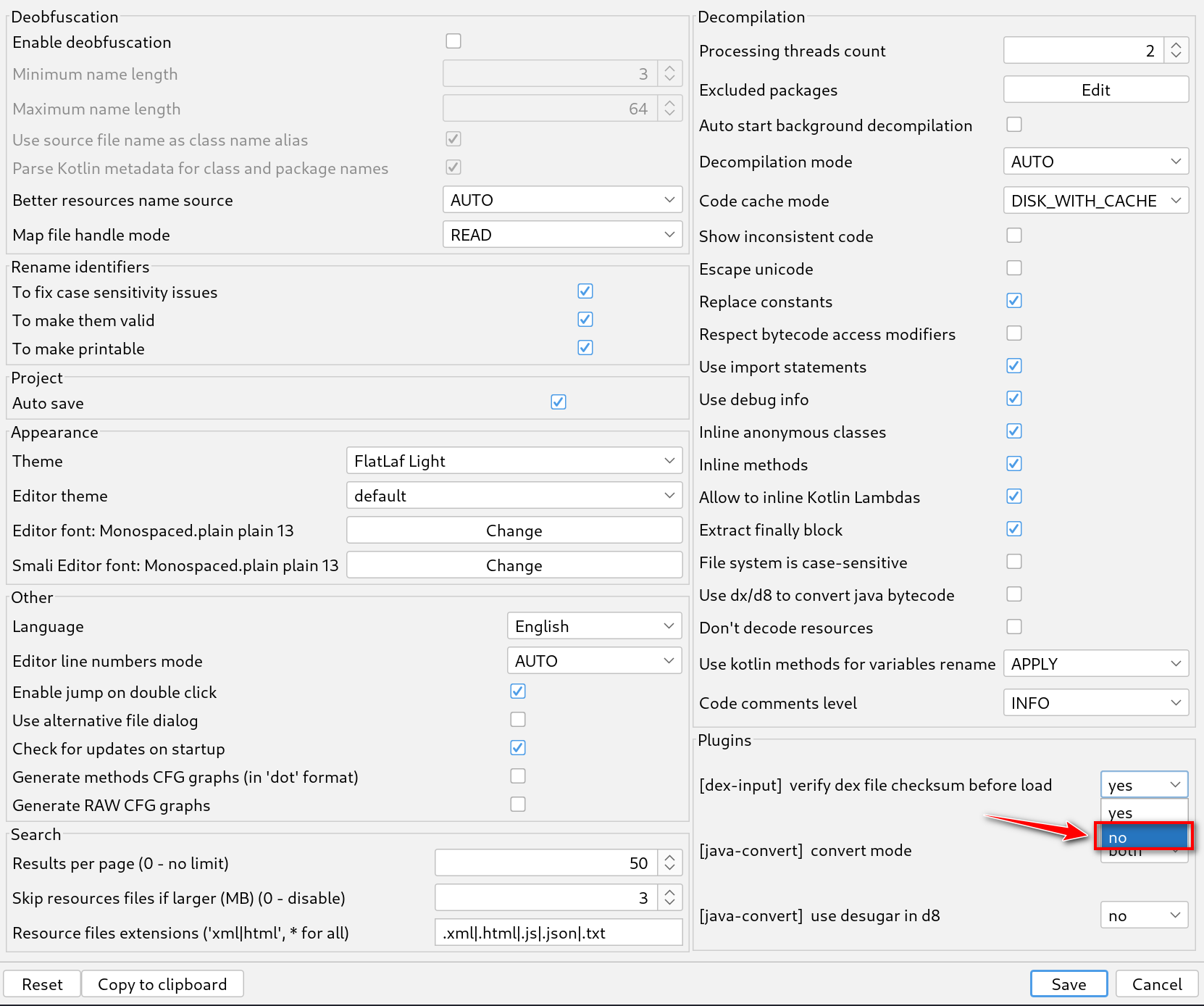
再重新打开一遍就可以正常显示了
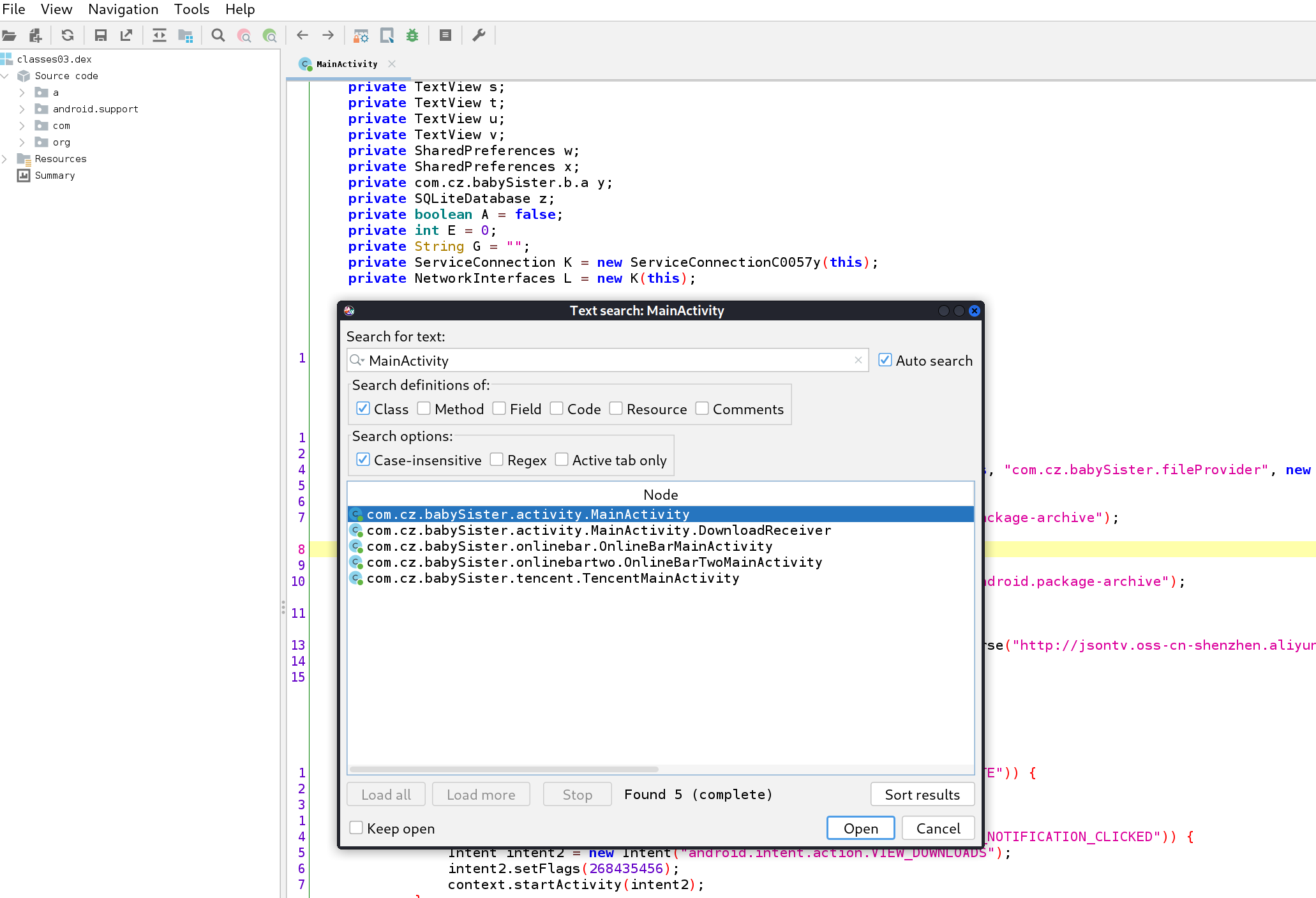
- 可以直接搜索定位到我们的MainActivity等方法
或者我们使用GDA工具也同样可以打开
参考文章:
本博客所有文章除特别声明外,均采用 CC BY-NC-SA 4.0 许可协议。转载请注明来源 xiaoeryu!
评论